

Facial Recognition and cybercrime: how easy is it to fool a biometric system?
We've already discussed the creation and use of Facial Recognition technology, the positive results of artificial intelligence testing, and the high efficiency rates of biometric systems. But how reliable and foolproof is this technology?
Can facial recognition systems be fooled?
It turns out they can. Some cases have garnered significant attention, and these are not the only examples of "bypassing" facial recognition systems.
Grigory Bakunov invented an algorithm that designs a unique random makeup to protect the user's face from being identified by facial recognition systems and to deceive the software. However, the developer decided not to market his product, realizing that the algorithm could be used by cybercriminals.
In Germany, Berlin-based artist Adam Harvey devised a similar algorithm called CV Dazzle. It creates clothing with special patterns (depicting eyes and mouths on the fabric) that helps avoid detection and identification by video analytics systems, thus confusing facial recognition technology.
At the end of 2017, a Vietnamese company successfully used a mask to hack the Face ID facial recognition feature in Apple's iPhone X. However, this method proved too complex for mass adoption, preventing its widespread use (including for malicious purposes).
Around the same time, researchers from a German company discovered a vulnerability that allowed them to bypass Windows 10 Hello authentication simply by printing an image of a face in the infrared spectrum.
In May 2018, Forbes reported that researchers from the University of Toronto developed an algorithm that disrupts facial recognition technology by altering certain pixels in an image. These changes are imperceptible to the human eye but can confuse facial recognition algorithms.
Naturally, such a number of vulnerabilities could not go unnoticed. Currently, security experts are working on creating effective mechanisms to combat spoofing—substituting faces and deceiving biometric systems.
Solving the problem of fooling facial recognition technology
Experts identify two algorithms whose implementation would make facial recognition systems less vulnerable:
- Liveness Check: The facial recognition system must ensure that the captured image is that of a real person, not a photograph (2D), smartphone screen, tablet, or any other electronic device (2D), or a mask (3D).
- Image Consistency Check: The system must be able to determine that the facial images of two or more people have not been merged into one and used in identity documents.
Enhancing these mechanisms will be a priority for facial recognition system algorithm developers in the near future. Implementing these developments will help curb spoofing and make biometric systems more reliable.
What's New?
All news
TRASSIR at Securex 2026 with neaMetrics
TRASSIR at Securex 2026 with neaMetrics

Ensuring guest safety in hotel lobbies and common areas
Ensuring guest safety in hotel lobbies and common areas

Monitoring playground and sports areas for children’s safety
Monitoring playground and sports areas for children’s safety

TRASSIR & ZNA Teknoloji at Retail Days İstanbul 2026: Powering the next era of smart retail
TRASSIR & ZNA Teknoloji at Retail Days İstanbul 2026: Powering the next era of smart retail

TRASSIR FMPA — secure your facility 24/7
TRASSIR FMPA — secure your facility 24/7

Protecting high-value industrial equipment from theft
Protecting high-value industrial equipment from theft

AI video insights for retail inventory management and loss prevention
AI video insights for retail inventory management and loss prevention

TRASSIR introduces FMPA — Face Match Passage Analysis
TRASSIR introduces FMPA — Face Match Passage Analysis

Improving visitor flow in museums and galleries with smart video analytics
Improving visitor flow in museums and galleries with smart video analytics
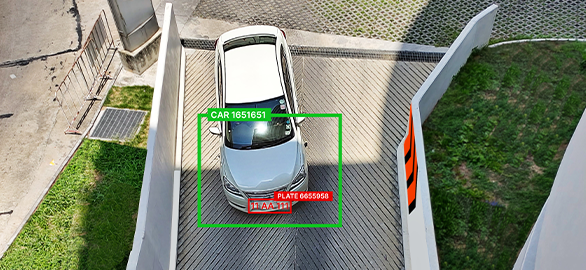
Why camera setup matters for license plate recognition — and how to get it right
Why camera setup matters for license plate recognition — and how to get it right

How video analytics help reduce workplace accidents in factories
How video analytics help reduce workplace accidents in factories

Industrial facility in the UAE enhances safety compliance with TRASSIR AI analytics
Industrial facility in the UAE enhances safety compliance with TRASSIR AI analytics

Predictive maintenance in real estate using video data
Predictive maintenance in real estate using video data

TRASSIR introduces Weight View — automated vehicle weight monitoring script
TRASSIR introduces Weight View — automated vehicle weight monitoring script

Preventing theft of high-value medicines in pharmacies
Preventing theft of high-value medicines in pharmacies

Food production facility enhances security with centralized TRASSIR surveillance
Food production facility enhances security with centralized TRASSIR surveillance

Kipaş Kağıt Fabrikası upgrades perimeter security with TRASSIR
Kipaş Kağıt Fabrikası upgrades perimeter security with TRASSIR

Combining POS and video analytics to reduce errors at the counter
Combining POS and video analytics to reduce errors at the counter

Leading textile manufacturer enhances security and operational efficiency with TRASSIR
Leading textile manufacturer enhances security and operational efficiency with TRASSIR
Try TRASSIR For Your Business
Learn more about how TRASSIR analytic modules work! Demo mode is an opportunity to see for yourself how the system works, and also check the interface and test all the functions.Success!
We will contact you as soon as possible