

Safeguarding Your Security Cameras from Hackers
In today’s digital landscape, home security systems face a novel and troubling threat. Hackers are increasingly targeting home surveillance cameras, using them to stage false emergencies. This alarming trend includes a dangerous prank known as “swatting,” where individuals falsely report violent incidents to provoke police intervention.
The implications of such actions can be dire. For instance, in 2017, a man lost his life when police, acting on a fraudulent report, forcibly entered his home. This incident highlights the need to protect devices intended for safety from malicious actors. To help prevent such abuses, we’ve compiled several strategies to enhance the security of your surveillance system.
Hackers exploit various vulnerabilities in security cameras to access private footage. Techniques range from stealing login credentials from breached websites to infiltrating your home router, allowing them to manipulate connected devices. Since the sophistication of hackers can vary significantly, it’s crucial to implement robust security measures for all your devices, particularly your cameras.
One of the most common methods hackers use to breach security systems is through credentials obtained from previous data leaks. Alarmingly, over 50% of internet users admit to reusing passwords or only slightly altering a single password for multiple accounts.
To enhance security, ensure that you use unique passwords for different accounts. Each password should be complex, incorporating a mix of lowercase and uppercase letters, numbers, and special characters, such as symbols or punctuation. The longer and more intricate your password, the more challenging it will be for hackers to decipher. Additionally, avoid using easily accessible personal information that might be discoverable online or via social media.
While you can create strong passwords independently, employing a password manager is a highly recommended approach. These tools generate robust, random passwords for your accounts and store them securely. With a single strong login for your password manager, you can manage all your credentials conveniently and safely.
Setting up two-factor authentication (2FA) may require some technical knowledge, but it offers a powerful extra layer of security. This feature mandates that users input a second, randomly generated code upon logging into their security cameras.
While some security service providers include 2FA by default, others may not offer this feature. You can receive SMS codes automatically for certain logins or use authentication apps that generate codes that refresh every few minutes.
Security systems are increasingly targeted by hackers, making it essential to take proactive measures to protect them. One of the primary concerns with IP cameras is their constant internet connectivity, which exposes them to ongoing hacking attempts. Currently, no security camera brand can confidently claim to be completely immune to hacking.
However, engaging a professional installer can significantly minimize vulnerabilities. Experts possess the necessary knowledge of various security systems and their operating software, enabling them to help secure your cameras effectively. They can guide you toward security products with enhanced encryption, assist in password management, ensure that firmware is updated, and change the default security settings of your system. When it comes to protecting your home surveillance setup, relying on professional expertise can be invaluable.
Articles
All articles
Supply Chain Cybersecurity: How TRASSIR Reduces Logistics Ransomware Risk by 65%
Supply Chain Cybersecurity: How TRASSIR Reduces Logistics Ransomware Risk by 65%

AI Warehouse Surveillance: How TRASSIR Cuts Theft by 30% in 2025
AI Warehouse Surveillance: How TRASSIR Cuts Theft by 30% in 2025
Construction Site Equipment Tracking: Preventing Million-Dollar Losses Through Advanced Logistics Solutions
Construction Site Equipment Tracking: Preventing Million-Dollar Losses Through Advanced Logistics Solutions

Zero Trust Security for Modern Supply Chain Operations: How TRASSIR Transforms Logistics Cybersecurity
Zero Trust Security for Modern Supply Chain Operations: How TRASSIR Transforms Logistics Cybersecurity
Real-Time Vehicle Monitoring: Enhancing Fleet Security with GPS and Cameras
Real-Time Vehicle Monitoring: Enhancing Fleet Security with GPS and Cameras

Preventing Cargo Theft: Advanced Security Solutions for Logistics Centers
Preventing Cargo Theft: Advanced Security Solutions for Logistics Centers

Video Analytics for Inventory Management: Streamlining Operations with TRASSIR's Intelligent Solutions
Video Analytics for Inventory Management: Streamlining Operations with TRASSIR's Intelligent Solutions

Drone Surveillance Technology: Revolutionizing Logistics Site Security
Drone Surveillance Technology: Revolutionizing Logistics Site Security
Smart Warehouse Monitoring: IoT Solutions for Real-Time Asset Tracking Transform Logistics Operations
Smart Warehouse Monitoring: IoT Solutions for Real-Time Asset Tracking Transform Logistics Operations

Predictive Analytics for Warehouse Safety: Reducing Accidents with AI
Predictive Analytics for Warehouse Safety: Reducing Accidents with AI

The Advantages of a Comprehensive Home Surveillance System
The Advantages of a Comprehensive Home Surveillance System

Seeing Clearly: The Advantages of 4K Surveillance for Businesses
Seeing Clearly: The Advantages of 4K Surveillance for Businesses

Indoor vs. Outdoor Security Cameras: Making the Right Choice for Your Safety
Indoor vs. Outdoor Security Cameras: Making the Right Choice for Your Safety

The Smart Investment: How Monitored Security Cameras Enhance Business Safety
The Smart Investment: How Monitored Security Cameras Enhance Business Safety

2024 Security Camera Buying Guide: What You Need to Know
2024 Security Camera Buying Guide: What You Need to Know

Essential Guide to Troubleshooting IP Camera Systems
Essential Guide to Troubleshooting IP Camera Systems

Artificial Intelligence: Transforming IP Camera Systems
Artificial Intelligence: Transforming IP Camera Systems
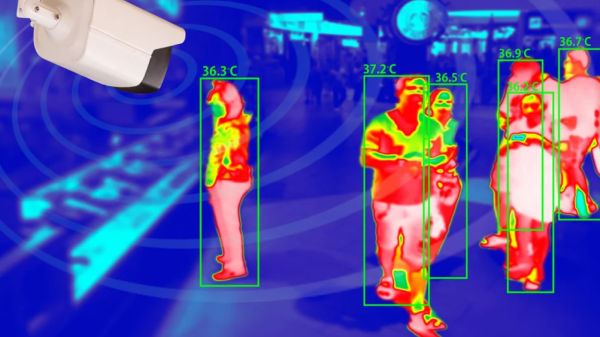
Thermal Cameras: Enhancing Security and Operational Excellence Across Industries
Thermal Cameras: Enhancing Security and Operational Excellence Across Industries

Maximizing Safety and Efficiency: The Impact of IP Camera Systems Across Industries
Maximizing Safety and Efficiency: The Impact of IP Camera Systems Across Industries

Beyond Security: How Surveillance Cameras Transform Shipping and Receiving Operations
Beyond Security: How Surveillance Cameras Transform Shipping and Receiving Operations
Try TRASSIR For Your Business
Learn more about how TRASSIR analytic modules work! Demo mode is an opportunity to see for yourself how the system works, and also check the interface and test all the functions.Success!
We will contact you as soon as possible